Researchers at the Rutgers University have developed a unique system to safeguard your computer and online accounts by using images, and not digits and alphabets as passwords.
In one of the solutions proposed by the group, the user is required to pick certain 'click-points' that he had selected initially while setting the password on an an image. The other solution requires the user to select certain icons scrambled within hundreds of icons and then click inside the "convex hull" formed by connecting imaginary lines among these selected icons.
In the first method, the user sets the password by selecting an image of his choice and then selecting a number of regions in that picture. Now to authenticate himself, he will have to click within those regions in the picture.

Example: To login, the user is required to click within the 4 circled red regions in this picture.
The second method requires the user to select a number of pass-icons from a large pool of icons and memorize them. Now to authenticate himself, the user will have to locate a minimum of three pass-icons from the randomly moving icons pool and click anywhere inside the "convex hull" formed by connecting imaginary lines among these pass icons. The user is required to click inside these regions perform this a predefined number of times and only then is he defined access.
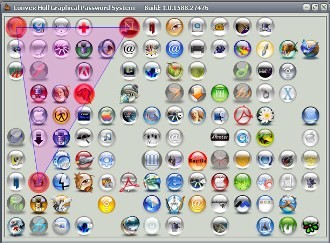
Icon Based Graphical Password: The user has to click inside the area shown here as highlighted
Visit:
The Graphical Password Project Homepage
Graphical passwords for better security
In one of the solutions proposed by the group, the user is required to pick certain 'click-points' that he had selected initially while setting the password on an an image. The other solution requires the user to select certain icons scrambled within hundreds of icons and then click inside the "convex hull" formed by connecting imaginary lines among these selected icons.
In the first method, the user sets the password by selecting an image of his choice and then selecting a number of regions in that picture. Now to authenticate himself, he will have to click within those regions in the picture.

Example: To login, the user is required to click within the 4 circled red regions in this picture.
The second method requires the user to select a number of pass-icons from a large pool of icons and memorize them. Now to authenticate himself, the user will have to locate a minimum of three pass-icons from the randomly moving icons pool and click anywhere inside the "convex hull" formed by connecting imaginary lines among these pass icons. The user is required to click inside these regions perform this a predefined number of times and only then is he defined access.
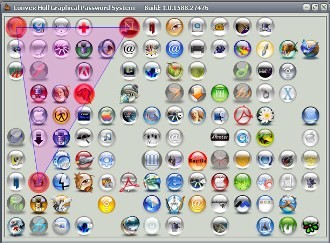
Icon Based Graphical Password: The user has to click inside the area shown here as highlighted
Visit:
The Graphical Password Project Homepage
Graphical passwords for better security
Comments